-
Transcript
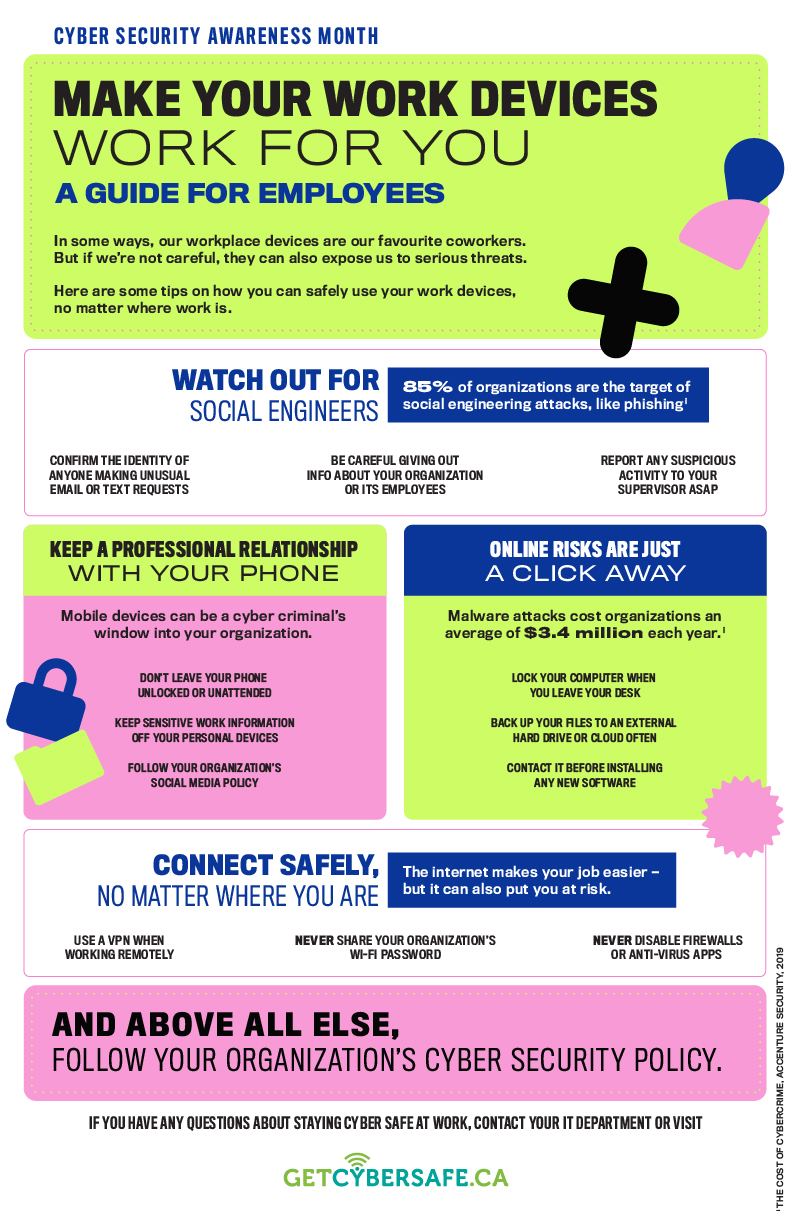
Cyber Security Awareness Month
Make your work devices work for you
A guide for employeesIn some ways, our workplace devices are our favourite coworkers. But if we’re not careful, they can also expose us to serious threats.
Here are some tips on how you can safely use your work devices, no matter where work is.
Watch out for social engineers
85% of organizations are the target of social engineering attacks, like phishingNote iConfirm the identity of anyone making unusual email or text requests
Be careful giving out info about your organization or its employees
Report any suspicious activity to your supervisor ASAPKeep a professional relationship with your phone
Mobile devices can be a cyber criminal’s window into your organization.Don’t leave your phone unlocked or unattended
Keep sensitive work information off your personal devices
Follow your organization’s social media policyOnline risks are just a click away
Malware attacks cost organizations an average of $3.4 million each year.Note iLock your computer when you leave your desk
Back up your files to an external hard drive or cloud often
Contact IT before installing any new softwareConnect safely, no matter where you are
The internet makes your job easier — but it can also put you at risk.Use a VPN when working remotely
Never share your organization’s Wi-Fi password
Never disable firewalls or anti-virus appsAnd above all else, follow your organization’s cyber security policy.
If you have any questions about staying cyber safe at work, contact your IT department or visit GETCYBERSAFE.CA
- i
The Cost of Cybercrime, Accenture Security, 2019
- i